Content:
- Introduction: S3 Bucket Security
- Understand AWS S3 Bucket Security Features
- Implement Lifecycle Policies of S3 Bucket Security
- Enable MFA Delete for AWS S3 Bucket Security
- Use S3 Block Public Access
- Enable S3 Object Lock
- Implement S3 Bucket Security Logging Process
- AWS S3 Bucket Security Policy
- Review and Update Permissions for S3 Bucket Security
- Implement S3 Bucket Security Tagging
- Concern about Cloud Storage Security
- Developing a Data Loss Prevention (DLP) Strategy
- Incident Response Planning
- Backup and Disaster Recovery
- The Importance of Regulatory Compliance
- Monitor and Audit S3 Bucket Security Activity
- Conclusion: S3 Bucket Security Best Practices
- FAQs:
Introduction: S3 Bucket Security
Securing your data stored in Amazon S3 is crucial for protecting your organization’s sensitive information. In this guide, we’ll walk you through the essential AWS S3 Bucket security best practices you should implement to safeguard your data and ensure compliance with industry standards.
Understand AWS S3 Bucket Security Features
AWS S3 offers a range of security features to help you protect your data, including access control, encryption, and logging. Therefore, you must familiarize yourself with these features and how to configure them to meet your organization’s security requirements.
- Access Control: Implement IAM policies, bucket policies, and access control lists (ACLs) to regulate access to your S3 buckets and objects.
- Encryption: Utilize server-side or client-side encryption to guarantee data remains encrypted at rest and in transit.
- Logging: Enable S3 access logging to monitor and record all actions taken on your S3 resources. Consequently, this enables the detection and investigation of any potentially suspicious activity.
Implement Lifecycle Policies of S3 Bucket Security
Use S3 lifecycle policies to automatically manage the lifecycle of your objects, such as by transitioning them to lower-cost storage classes or deleting them after a certain period. Consequently, this can help you reduce storage costs and ensure compliance with data retention policies.
For example, you could create a lifecycle policy to move objects older than 90 days to the Glacier storage class. Subsequently, you can delete these objects after 365 days.
Check this below video to get more insight about Amazon S3 security:
Enable MFA Delete for AWS S3 Bucket Security
Enable the “MFA Delete” feature to add an extra layer of security to your S3 buckets. This action requires users to provide a valid multi-factor authentication (MFA) code before permanently deleting an object or changing a bucket’s versioning state.
To enable MFA Delete, navigate to the S3 console, select your bucket, and access the “Properties” tab. Under the “Versioning” section, opt to “Enable MFA Delete.
Use S3 Block Public Access
By default, S3 buckets and objects are set to private access. However, users can accidentally make them publicly accessible, which can lead to data breaches. Likewise, to prevent this, utilize the S3 Block Public Access feature to block public access to your S3 resources.
Furthermore, depending on your specific security requirements, you can implement this feature on the account, bucket, or both.
Enable S3 Object Lock
S3 Object Lock allows you to prevent objects from being deleted or overwritten for a specified retention period. Therefore, this can be useful for compliance requirements, such as those related to the SEC Rule 17a-4(f) or FINRA Rule 4511(c).
To enable Object Lock, navigate to the S3 console, create a new bucket or select an existing one, and then activate the “Object Lock” setting in the bucket properties.
Implement S3 Bucket Security Logging Process
| Enable S3 Access Logging | Enable S3 Access Logging to track all actions performed on your S3 resources. This can help detect and investigate suspicious activity. |
| Use CloudTrail Logging | Utilize CloudTrail Logging to track all API calls made to your AWS resources, including S3. Consequently, this can offer valuable information for security and compliance purposes. |
| Centralize Logging | Additionally, centralize logging. You might consider a secure, managed service like Amazon CloudWatch or a third-party logging platform. Thus, you can enhance visibility and analysis. |
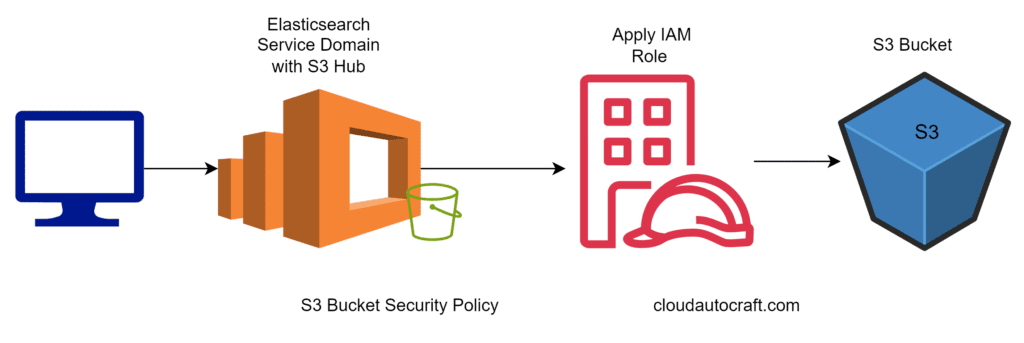
AWS S3 Bucket Security Policy
One common vector for data breaches is unauthorized access to Amazon S3 buckets, cloud-based storage solutions. In a recent incident, an attacker gained access to an S3 bucket containing sensitive customer data, leading to a devastating data breach. Consequently, it’s essential to configure and secure your S3 buckets properly to prevent such incidents.
- Access Control:
- First, implement strict access controls to your S3 buckets, limiting permissions to only those who need them. Moreover, regularly review and audit your access policies to ensure they are up-to-date and secure..
- Encryption:
- Additionally, enable server-side encryption for your S3 buckets to protect your data at rest. This step ensures that the data will be unreadable without encryption keys even if an attacker gains access.
- Monitoring and Logging:
- Finally, set up comprehensive monitoring and logging for your S3 buckets. This will allow you to detect and respond quickly to unauthorized access attempts.
Review and Update Permissions for S3 Bucket Security
Review the permissions granted to your IAM users, roles, and groups regularly and update them as needed to ensure they align with your security requirements. This practice is critical when employees join, leave, or change organisational roles.
Utilize tools such as the AWS Identity and Access Management (IAM) Access Analyzer to help identify unused or overly permissive permissions and facilitate the necessary adjustments.
Implement S3 Bucket Security Tagging
| Organizing Buckets: | Automating Policies: | Enabling Cost Optimization: |
| Utilize bucket tagging to categorize your S3 resources. This helps implement suitable security and access controls. Consequently, it facilitates the swift identification and administration of sensitive data. | Utilize bucket tags to enforce security policies automatically. For example, you can apply lifecycle rules, encryption configurations, and access controls. | Leverage tags to identify and manage idle or underutilized buckets. As a result, this aids in optimizing your S3 storage expenses. |
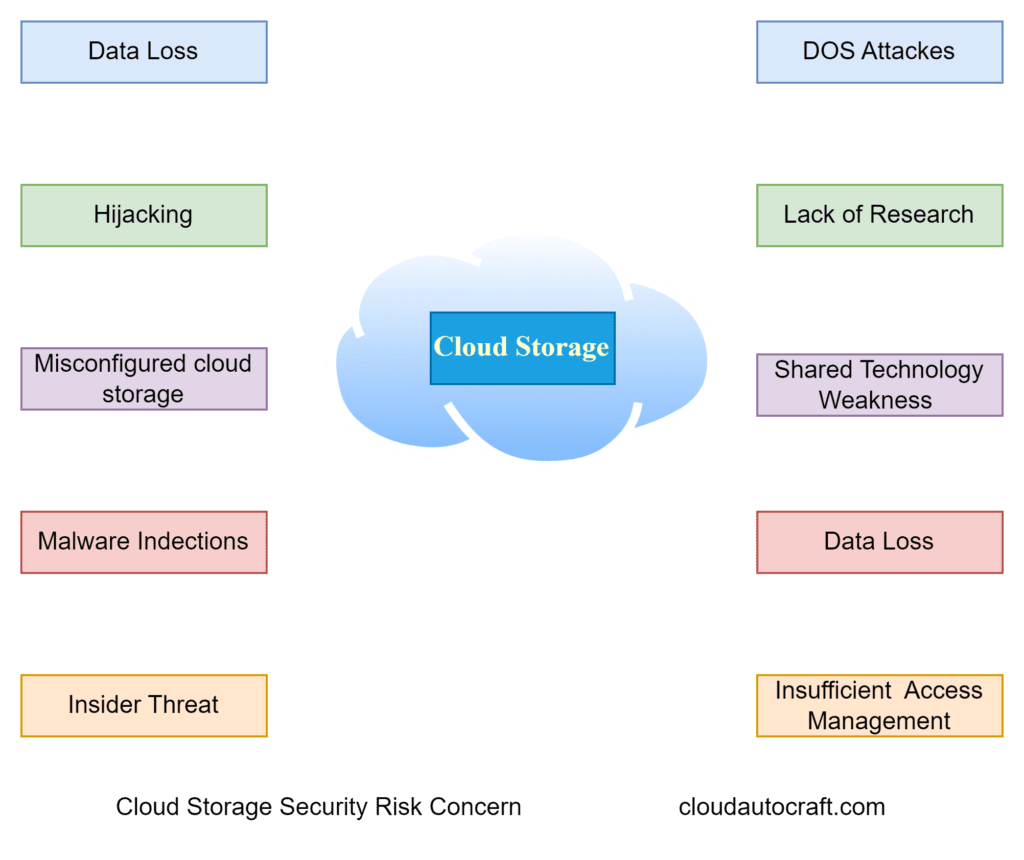
Concern about Cloud Storage Security
While cloud storage offers many benefits, it also comes with inherent risks. For instance, misconfigured access controls or weak security protocols can leave your sensitive data vulnerable to unauthorized access. Therefore, it’s essential to implement robust security measures to safeguard your valuable data.
Developing a Data Loss Prevention (DLP) Strategy
In addition to securing your S3 buckets, it’s crucial to have a robust data loss prevention (DLP) strategy in place. DLP measures help you identify, monitor, and protect sensitive data from unauthorized access or accidental loss.
| Identify Sensitive Data | First, identify the sensitive data within your organization. Consequently, this includes customer information, financial records, intellectual property, and other data that could be damaging if compromised. This step is crucial in developing a DLP strategy. |
| Monitor and Protect | Next, implement DLP solutions to monitor the flow of sensitive data. These solutions should protect data from unauthorized access or accidental loss. For example, consider using data encryption, access controls, and real-time data activity monitoring. |
| Employee Education | Furthermore, educate your employees on the importance of data security and their role in protecting sensitive information. Provide training on best practices for handling and securing data and how to identify and report potential threats. |
Incident Response Planning
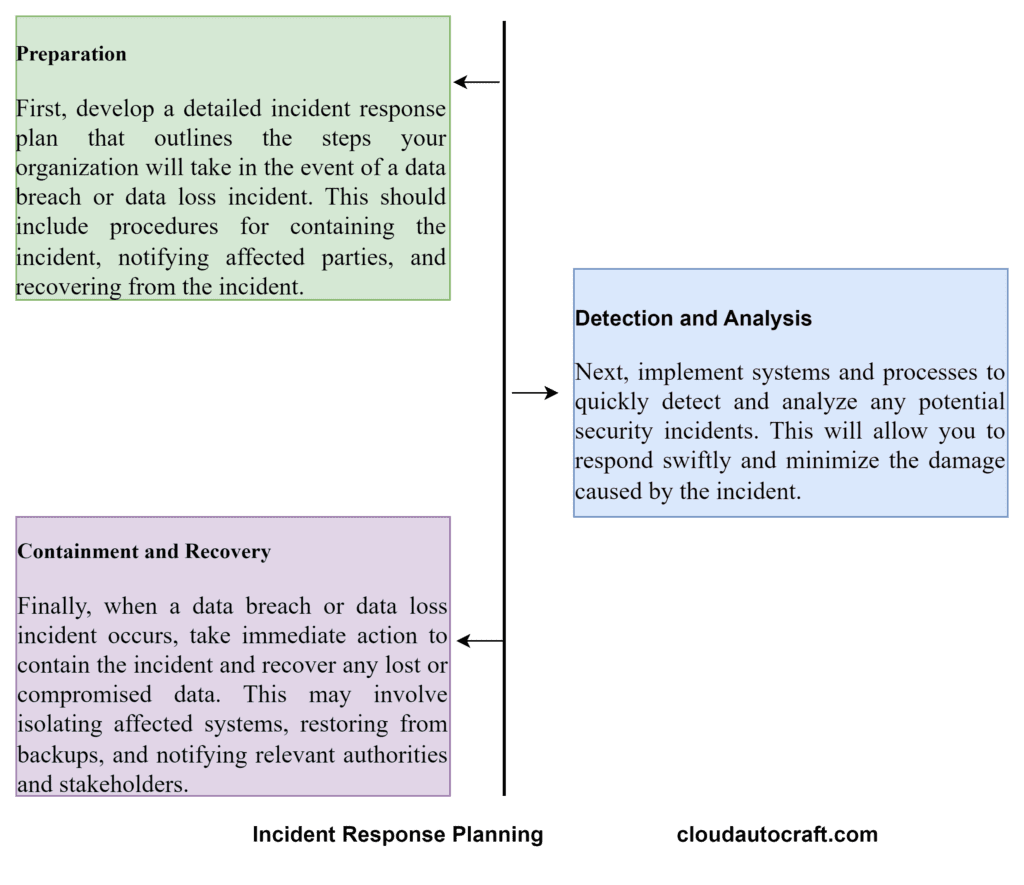
Even with robust security measures, the possibility of a data breach or loss incident can never be eliminated. Therefore, it’s essential to have a comprehensive incident response plan to quickly and effectively respond to and mitigate the impact of a security incident.
Backup and Disaster Recovery
In the event of a data loss incident, it is crucial to have a robust backup and disaster recovery plan in place. Consequently, this will ensure that you can quickly restore your data. As a result, you can minimize the impact on your business operations.
Frequent Backups: First, make sure you’re backing up your data often. Regular backups mean you won’t lose important information if something goes wrong.
Disaster Recovery Plan: Next put together a solid disaster recovery plan. This plan should clearly explain what to do if something big happens, like a natural disaster or a ransomware attack. It helps your organization get back on track quickly.
Test and Validate: Finally, don’t just set it and forget it. Regularly test and validate your backup and disaster recovery processes. This way, you know they work when you need them most. Testing helps you catch and fix problems before they become real issues.
The Importance of Regulatory Compliance
Depending on your industry and the type of data you handle, you may be subject to various regulatory requirements, such as HIPAA, PCI DSS, or GDPR. Failing to comply with these regulations can result in significant fines, legal penalties, and damage caused by a data breach or data loss incident.
| Regulation | Description | Penalties |
| HIPAA | Protects the privacy and security of personal health information | Up to $50,000 per violation, with a maximum of $1.5 million per year |
| PCI DSS | Sets standards for the secure handling of credit card information | Fines up to $100,000 per month, plus potential revocation of the ability to process credit card payments |
| GDPR | Protects the personal data of EU citizens | Up to 4% of annual global revenue or €20 million, whichever is greater |
Monitor and Audit S3 Bucket Security Activity
Enabling CloudTrail
Activate AWS CloudTrail to monitor all API calls made to your S3 resources, capturing details such as the caller’s identity, actions performed, and timestamps of the activities.
Integrating with Security Tools
Explore integrating your S3 logging with security solutions like Amazon GuardDuty. Consider using third-party SIEM (Security Information and Event Management) platforms. This enhances visibility into your environment and helps automate the detection of security threats.
Conclusion: S3 Bucket Security Best Practices
To ensure AWS S3 bucket security, implement robust access controls. Additionally, use encryption and enable versioning. Furthermore, monitoring and logging activities are done to maintain oversight. Stay compliant with regulatory requirements to avoid potential issues. Moreover, utilize tools like AWS Trusted Advisor. Finally, implement MFA for additional security.
Click here to Read more about DevOps-Security – 2024 && Cyber Security – 2024
FAQs:
How can we manage S3 bucket permissions to prevent unauthorized access?
Answer: We can implement IAM policies, bucket policies, and access control lists (ACLs) to regulate access to S3 buckets. Additionally, regularly reviewing and updating permissions ensures security.
What encryption practices should we follow to secure data in S3 buckets?
Answer: We can use server-side encryption to secure data at rest (SSE-S3, SSE-KMS, SSE-C). Implementing SSL/TLS encryption for data in transit is also essential.
How do we enable and manage versioning for S3 buckets effectively?
Answer: Enabling versioning on S3 buckets helps maintain object history. Moreover, implementing lifecycle policies ensures efficient management of object versions. Additionally, it aids in compliance and minimizes storage costs.
Which tools should we use for monitoring and logging S3 bucket activities?
Answer: We can utilize AWS CloudTrail to log comprehensive API activity. Furthermore, Integration with SIEM solutions enhances monitoring and threat detection capabilities.
Originally posted 2024-06-10 15:00:48.