Securing your AWS RDS databases is crucial for protecting sensitive data and maintaining compliance. This guide covers key Best Practices of AWS RDS Security, including network isolation, encryption, access control, monitoring, and more. By following these recommendations, you can significantly enhance the security posture of your RDS instances and safeguard your organization’s valuable information assets.
Content:
- Understanding AWS RDS Security Best Practices
- Implementing Network Security
- Encryption: Protecting Data at Rest and in Transit
- AWS RDS Security: Access Management and Authentication
- Monitoring & Auditing
- AWS RDS Security: Backup and Recovery tactics
- Keeping Your AWS RDS Security Instances Updated
- Implementing Database-Specific Security Measures
- AWS RDS Security Application Access
- Implementing Multi-AZ Deployments
- Using AWS Secrets Manager
- Implement Data Masking and Encryption
- Conclusion: A Holistic Approach to AWS RDS Security
- FAQs:
- What are most common AWS RDS Security risk, and how can they be mitigated?
- How can I ensure encryption is properly implemented for AWS RDS Security databases?
- What are the best practices for managing user access and permissions in AWS RDS Security?
- How can I set up effective monitoring and alerting for potential security breaches in AWS RDS?
Understanding AWS RDS Security Best Practices
Before diving into specific best practices, let’s cover the fundamentals of AWS RDS security. Amazon’s Relational Database Service (RDS) is a managed database offering. It supports multiple database engines. Security for RDS involves protecting your data at rest and in transit. Additionally, it includes controlling access and monitoring for potential threats.
AWS provides several built-in security features for RDS. However, it’s up to you to implement and configure them correctly. Remember that security is a shared obligation between AWS and you, the client. Therefore, let’s explore how to make the most of these features. We will also add additional layers of protection.
Implementing Network Security
Network security is the first line of defense for your RDS instances. Therefore, Ensuring that only authorized traffic reaches your databases is essential. Here’s how you can achieve this:
- Use Amazon VPC: Create an isolated environment for your RDS instances within Amazon Virtual Private Cloud (VPC).
- Configure Security Groups: Define security groups to control both inbound and outbound traffic to and from your RDS instances. Security groups function as virtual firewalls at the instance level.
- Implement Network ACLs: Add a layer of security with Network Access Control Lists (ACLs) at the subnet level. ACLs allow you to set rules for controlling traffic more granularly than security groups.
- VPN or AWS Direct Connect: Utilize VPN or AWS Direct Connect to establish secure connections between your on-premises networks and AWS. Consequently, this ensures encrypted and dedicated connections, enhancing security for transit data.
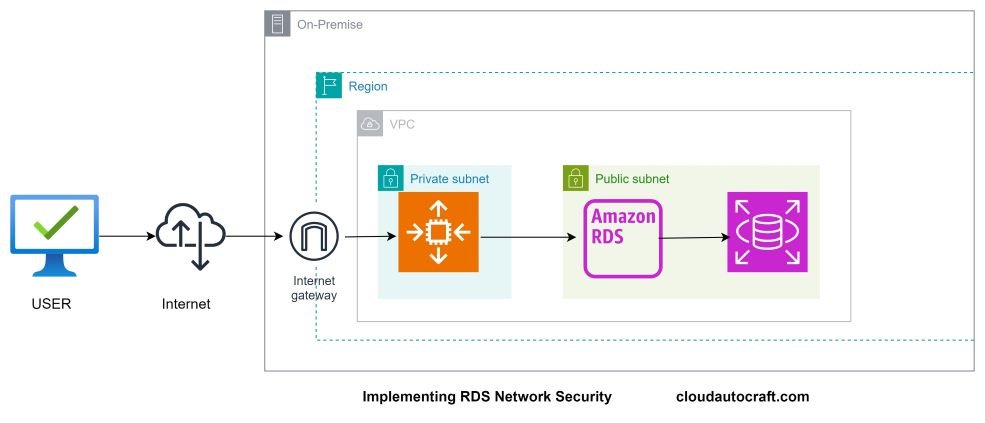
Consequently, You establish a robust foundation for your RDS security strategy by carefully configuring these network settings.
Encryption: Protecting Data at Rest and in Transit
Data at Rest:
Enable AWS KMS encryption for your RDS instances to secure data stored on disk. This safeguards your data against unauthorized access, even if there’s physical access to the storage media.
Data in Transit:
Ensure data integrity and confidentiality using SSL/TLS connections between your application and the RDS instance. This encryption method prevents interception and manipulation of data during transmission.
Key Management:
Maintain strong security practices by regularly rotating encryption keys. AWS Key Management Service (KMS) provides secure storage and management of keys, enhancing the overall security of your encryption strategy.
Encryption is a critical final defense layer if other security measures falter. Therefore, implementing encryption correctly is essential to safeguarding your data effectively.
Click here to get more insight about : How AWS RDS Encryption at Rest Enhances Information Security
AWS RDS Security: Access Management and Authentication
Controlling who can access your RDS instances and what actions they can perform is critical for security. Consequently, here are some best practices:
- Use AWS Identity and Access Management (IAM): Manage user access and permissions centrally through IAM. By doing so, you can assign permissions based on the principle of least privilege to ensure users have only the necessary access for their roles.
- Implement Least Privilege: Grant users the minimum permissions required to perform their tasks. Moreover, avoid granting excessive privileges that could lead to unintended access or actions.
- Enable Multi-Factor Authentication (MFA): Strengthen account security by requiring MFA for all users accessing RDS instances. In addition, MFA adds a layer of protection against unauthorized access, even in cases where passwords are compromised.
- Regular Audits and Reviews: Furthermore, Regularly audits IAM policies, roles, and user permissions. Ensure that permissions align with current business needs and that no unnecessary privileges exist.
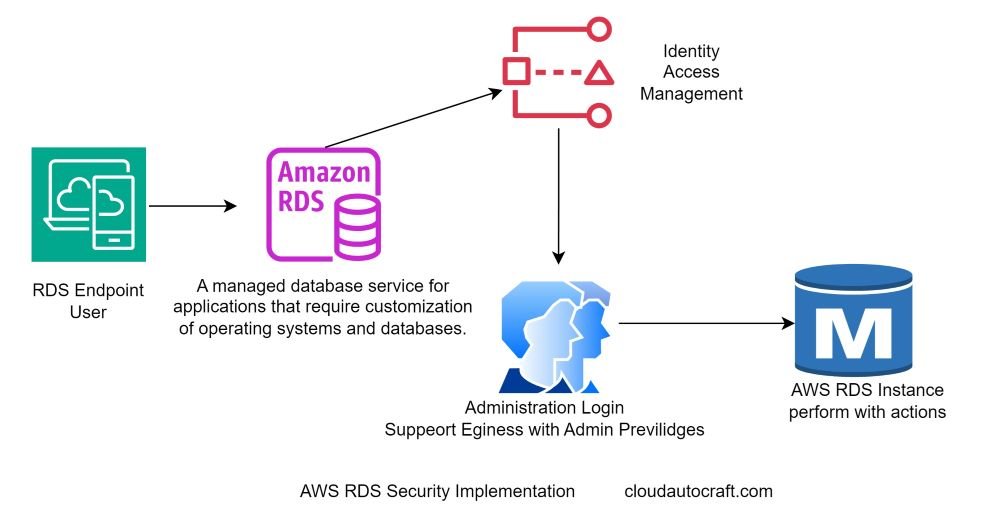
By implementing these strong access control measures, you enhance the security posture of your RDS instances, reducing the risk of unauthorized access and potential data breaches.
Monitoring & Auditing
Monitoring and auditing are essential for maintaining the security of your AWS RDS instances. AWS offers several tools and best practices to help you effectively monitor and audit your databases:
- Amazon CloudWatch: Utilize CloudWatch to monitor RDS performance metrics such as CPU utilization, storage usage, and throughput. Set alarms to receive notifications when metrics exceed predefined thresholds, enabling proactive response to potential issues.
- AWS CloudTrail: Enable CloudTrail to log API calls on your AWS account, including changes to RDS instances. CloudTrail provides a comprehensive audit trail that helps you track who did what and when aiding in forensic analysis and compliance auditing.
- Database-Specific Auditing Features: Using your database engine (e.g., MySQL, PostgreSQL), leverage native auditing features like MySQL audit plugin or PostgreSQL pgAudit. These tools capture detailed audit logs of database activities, including queries executed and changes made to data.
- Regular Review of Logs and Audit Trails: To ensure the security and integrity of your systems, establish a routine to regularly review CloudWatch metrics, CloudTrail logs, and database-specific audit logs. By doing this, you can systematically look for unusual or suspicious activity patterns. Consequently, this proactive approach may indicate potential security threats before they escalate. Furthermore, incorporating this routine into your operations will help maintain a vigilant stance against emerging risks.
Effective monitoring and auditing empower you to detect security incidents promptly and respond swiftly, reducing the impact of potential security breaches on your AWS RDS instances.
AWS RDS Security: Backup and Recovery tactics
While often overlooked in traditional security discussions, having a robust backup and recovery strategy is crucial for safeguarding your data against loss or corruption. Here’s what you should implement:
| Automated Backups: | Enable automated backups for your RDS instances. Consequently, AWS RDS allows you to schedule backups automatically, providing a straightforward way to recover data in case of accidental deletion, hardware failure, or other incidents. |
| Manual Snapshots: | Take regular manual snapshots of your RDS databases for additional protection. These manual snapshots offer a point-in-time recovery option, enabling you to restore to a specific state when needed. |
| Regular Testing of Recovery Process: | Regularly test your backup and recovery process to ensure it functions correctly. By simulating scenarios where you need to recover data, you can effectively verify that the process meets your recovery time objectives (RTOs) and recovery point objectives (RPOs). Additionally, this practice allows you to identify and address any issues before they impact your operations. |
| Cross-Region Replication: | Consider implementing cross-region replication for disaster recovery purposes. By replicating your RDS data to a different AWS region, you can provide additional redundancy. Consequently, this ensures data availability in case of regional outages or disasters. Furthermore, such a strategy enhances your overall data resilience and reliability. |
Recent backups and a tested recovery process can be crucial in a security breach or data loss incident. This will help restore your operations swiftly and minimize downtime. Moreover, this preparedness ensures that you can quickly respond to unexpected disruptions. As a result, you will maintain business continuity.
Keeping Your AWS RDS Security Instances Updated
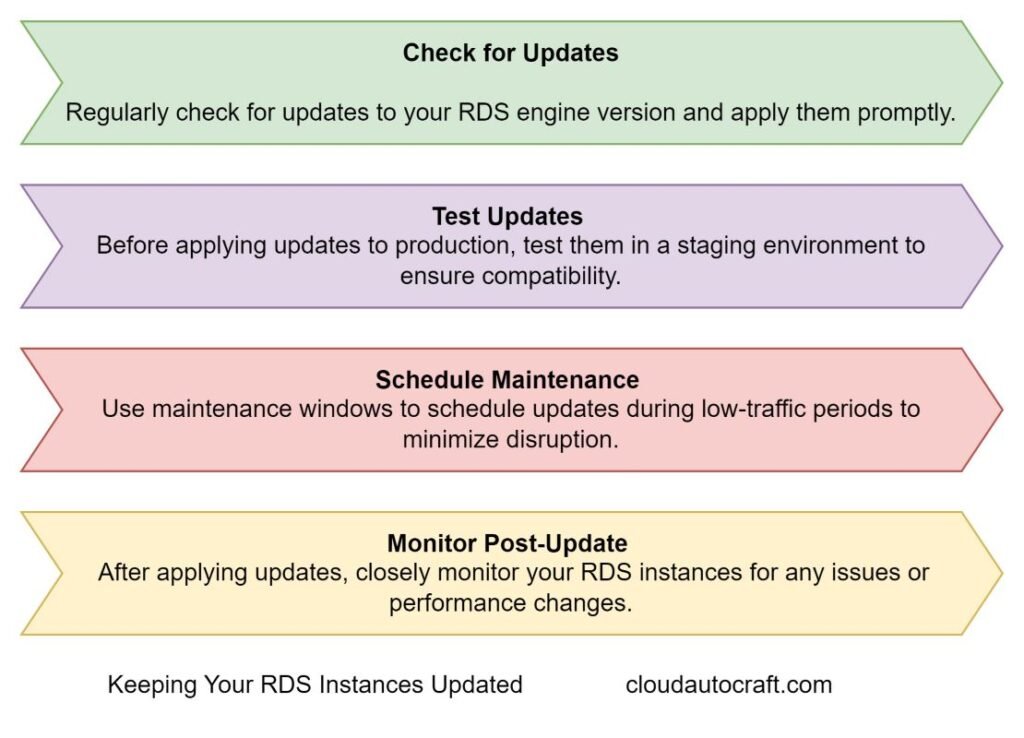
By keeping your RDS instances up-to-date, you protect against known vulnerabilities and ensure you have access to the latest security features and improvements provided by AWS.
Implementing Database-Specific Security Measures
Each database engine supported by AWS RDS has its security features and best practices. Here are examples tailored to different database engines:
| MySQL and MariaDB: | 1. Use SSL connections to encrypt data in transit between your applications and the database. 2. Enable the audit plugin to track and log database activity for compliance and security auditing purposes. |
| PostgreSQL: | 1. Implement Row-Level Security (RLS) to restrict access to rows based on certain conditions or policies. 2. Use pgAudit to capture detailed audit logs of database activities, helping to monitor and investigate potential security incidents. |
| Oracle: | Utilize Virtual Private Database (VPD) to implement fine-grained access control policies, restricting access to specific rows or columns based on user roles or conditions. |
| SQL Server: | Implement Transparent Data Encryption (TDE) to encrypt data at rest, providing an additional layer of protection against unauthorized access to your SQL Server database files |
It’s essential to familiarize yourself with the security features specific to your chosen database engine. Implement these features according to best practices. This ensures that your AWS RDS instances are secure. Additionally, it helps them remain compliant with your organization’s security policies and regulatory requirements.
AWS RDS Security Application Access
Your application’s interaction with RDS is a critical point to secure. Here are some best practices:
- Use IAM database authentication rather than storing database credentials in your application.
- Employ connection pooling to optimize the management of database connections.
- Use prepared statements to prevent SQL injection attacks.
- Before storing sensitive data in the database, ensure it is encrypted.
By following these steps, you ensure the security of the application database interface and close off a common attack vector for potential hackers.
Implementing Multi-AZ Deployments
Multi-AZ (Availability Zone) deployments are not just for high availability; they also enhance security. When you enable Multi-AZ, AWS automatically creates a replica of your database in a different AZ.
This provides several security benefits:
- Firstly, we need protection against hardware failures and AZ outages.
- Secondly, reduced risk of data loss due to physical infrastructure issues.
- Moreover, the ability to perform certain types of maintenance with minimal downtime.
While Multi-AZ does come with additional costs, the added security and peace of mind are often worth the investment.
Using AWS Secrets Manager
Managing database credentials can be challenging, especially in a dynamic environment.
AWS Secrets Manager can help:
- Securely store and manage database credentials.
- Automatically rotate credentials on a schedule.
- Control and audit access to secrets.
- Integrate with other AWS services for seamless secret retrieval.
By using Secrets Manager, you reduce the risk of credentials being exposed through configuration files or environment variables. Overall, it’s a powerful tool in your RDS security arsenal.
Implement Data Masking and Encryption
Protecting sensitive data within your database is crucial, especially when dealing with personally identifiable information (PII) or other confidential data.
Here are some strategies to implement:
Firstly, data masking techniques should be used to obscure sensitive information in non-production environments. Secondly, column-level encryption for sensitive data fields should be implemented. Use AWS Secrets Manager to securely store and manage database credentials and other secrets. Furthermore, homomorphic encryption should be considered for data that needs to be processed while remaining encrypted.
By implementing these data protection measures, you can ensure that sensitive information remains secure even if other security layers are compromised.
Conclusion: A Holistic Approach to AWS RDS Security
Securing your AWS RDS instances requires a multi-faceted approach. Network security, encryption, access management, and monitoring play crucial roles in protecting your data. Furthermore, security is an ongoing process, not a one-time setup. Therefore, regularly review and update your security measures to stay ahead of evolving threats.
Check out the official AWS RDS documentation for more information on AWS RDS security. Stay vigilant, keep learning, and prioritize security in all your database operations. By doing so, your data—and your users—will thank you for it.
Click here to Read more about DevOps-Security – 2024 && Cyber Security – 2024
FAQs:
What are most common AWS RDS Security risk, and how can they be mitigated?
Answer: Common risks such as unauthorized access and data breaches can be mitigated using strong passwords, enabling multi-factor authentication, and regularly updating our security settings. By maintaining these practices, we protect our data and systems.
How can I ensure encryption is properly implemented for AWS RDS Security databases?
Answer: Use AWS’s built-in encryption options, like encrypting data at rest and in transit. Additionally, always check that your encryption keys are managed securely.
What are the best practices for managing user access and permissions in AWS RDS Security?
Answer: Follow the principle of least privilege, regularly review user roles, and use IAM policies to control access. Additionally, logging is enabled to monitor user activities.
How can I set up effective monitoring and alerting for potential security breaches in AWS RDS?
Answer: Use AWS CloudWatch to monitor and set up suspicious activity alarms. Audit logs should also be regularly reviewed to detect any unusual behaviour.

1 thought on “AWS RDS Security Best Practices: What You Need to Know”